May 26th, 2026
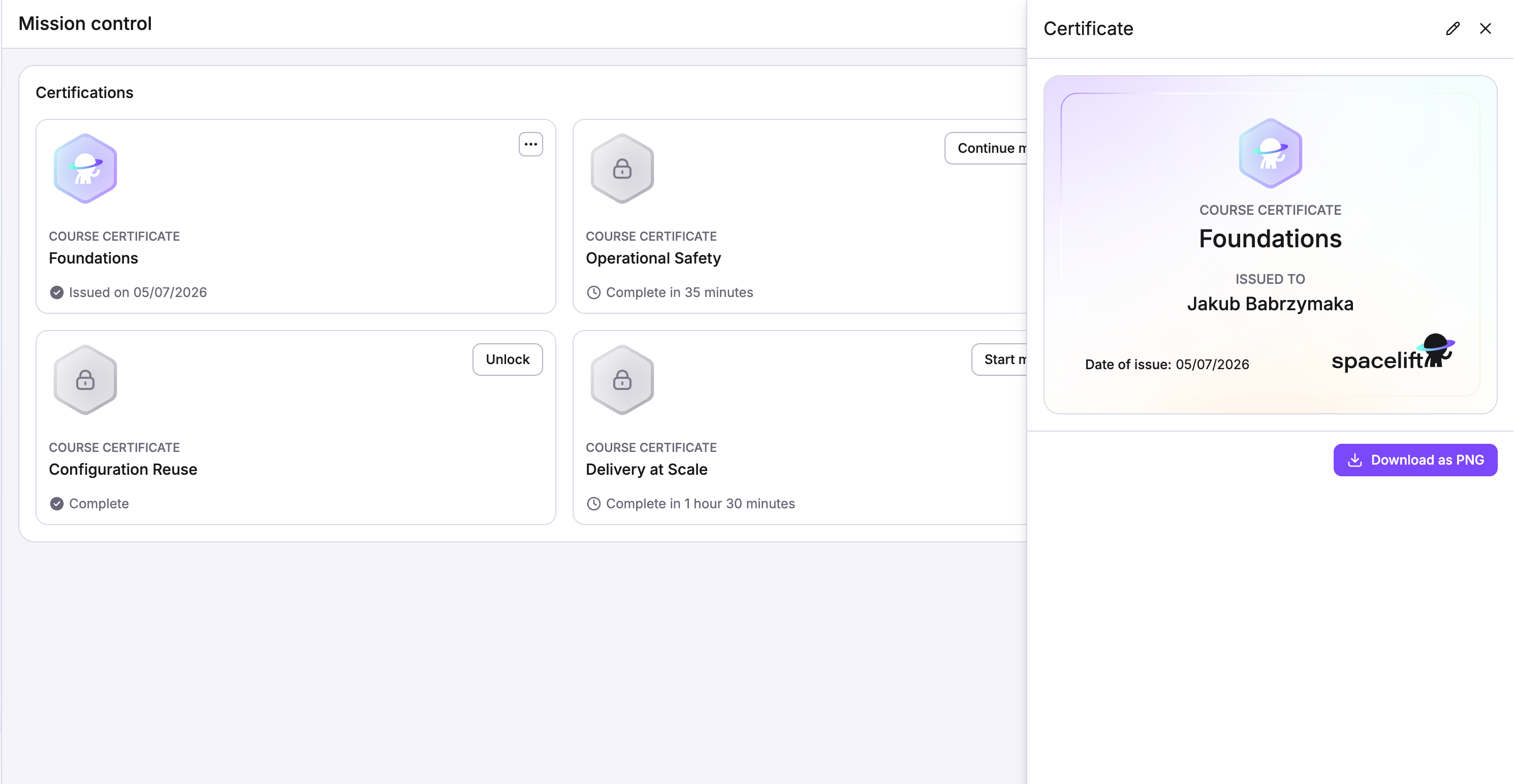
Have you been working hard since the new learning modules in the Launchpad came out? We know a lot of you have. And now, we’ve introduced a way to commemerate all your hard work, and celebrate your accomplishments! As you complete the learning modules, you can now view and download a certificate of completion. Your whole team can share in the pride as everyone gains more skills by completing missions, and collecting more certificates!
This update also brings the Launchpad and learning modules to even more users of the Spacelift platform. It’s not just admins who can see the Launchpad now. So be sure to check it out, complete some missions, and let us know what you think! Happy Learning!
Please Note: Some missions may not be available to all tiers, and some users may not have all the access needed to complete all of the missions.
May 18th, 2026
That’s right! You can now connect your LLM of choice directly to Spacelift using the new Remote MCP Server. If you already use AI-powered tools or agents for infrastructure work, this gives them a way to take action inside Spacelift, not just talk about it.
The Remote MCP Server works with any LLM or agent that supports the Model Context Protocol. Point it at Spacelift, and your existing tools can create and manage runs, query stack status, trigger deployments, and work with your infrastructure the same way you do in the UI or CLI.
A quick reminder on Infra Assistant modes
If you have not tried Infra Assistant recently, it now has two distinct modes:
Ask is read-only. You can query your infrastructure, ask questions about stack configurations, check run history, and get answers without changing anything. Good for investigation and context-gathering.
Build lets Infra Assistant take action. Give it instructions and it will create resources, trigger runs, and make changes in your infrastructure on your behalf. This is where the Remote MCP Server becomes especially useful: your own agents can operate in Build mode through the same interface.
Getting Started
Check out the docs for setup instructions and supported operations. If you run into questions or want help connecting a specific tool, reply to this email and we will get you sorted.
March 31st, 2026
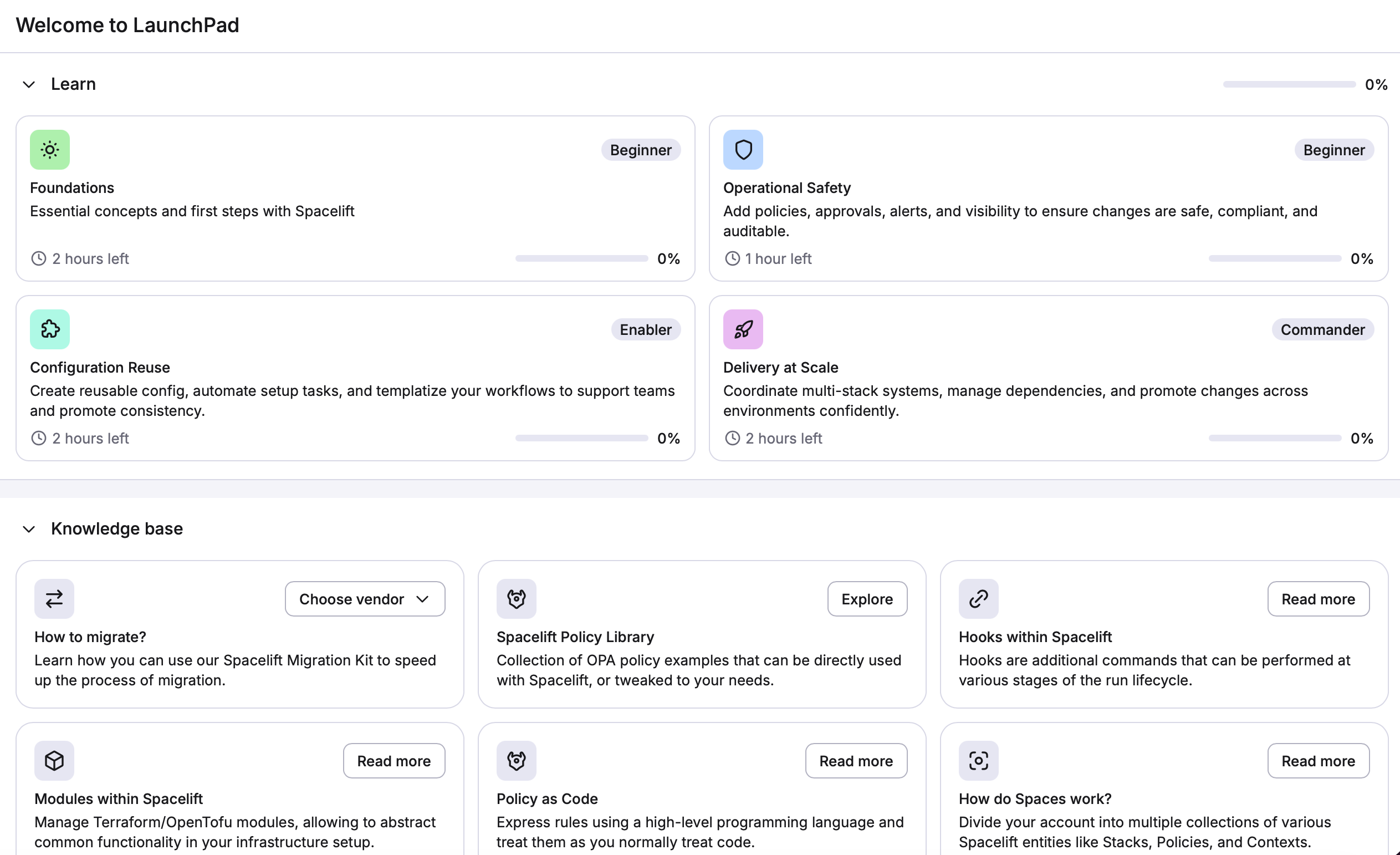
We've added a new and improved Learn section to the Spacelift Launchpad! It's a four-module, hands-on training experience built directly into the platform.
Note: This feature requires admin rights, as most of the tasks would require them.
What's new
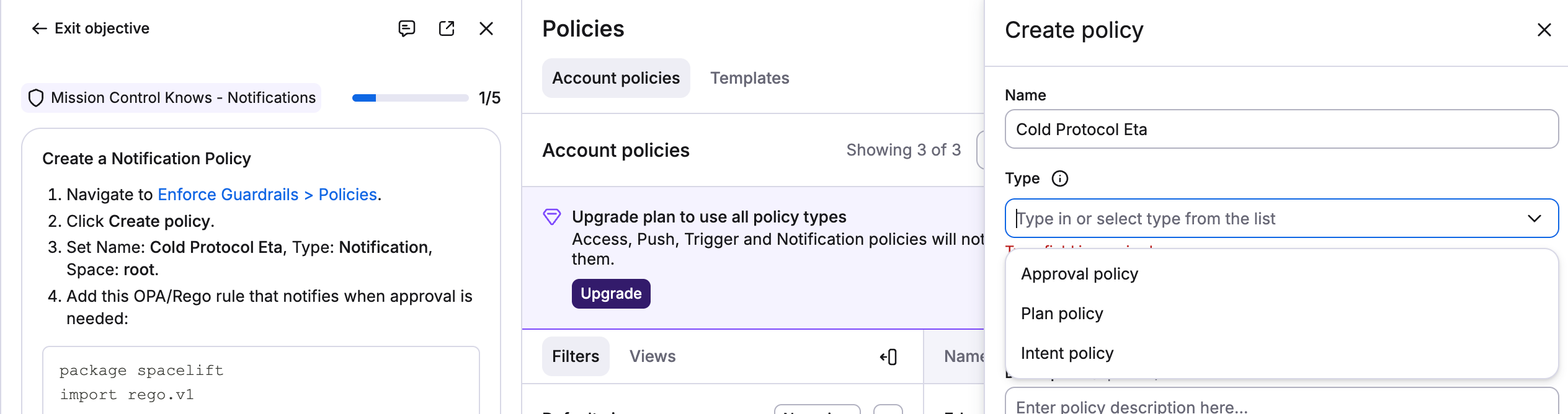
Launchpad Learn includes four modules:
Foundations — Essential concepts and first steps with Spacelift
Operational Safety — Policies, approvals, alerts, and audit visibility for safe, compliant changes
Configuration Reuse — Reusable config, automated setup, and templatized workflows for team-scale consistency
Delivery at Scale — Multi-stack coordination, dependency management, and confident environment promotion
Each module is divided into sections with sequential tasks. Tasks within a section must be completed in order, but you can move between sections freely. Every step includes code examples and everything else you need to complete it.
Who it's for
Launchpad Learn is designed for users at all levels. New users can work through Foundations to get operational quickly. Experienced users can start with whichever module matches what they're working on.
Where to find it
Go to Launchpad in your Spacelift account and open the Learn section. Check out the video here!
March 20th, 2026
We're making an improvement to how plan policies are evaluated for Terraform, OpenTofu, and Terragrunt stacks. Currently, when a plan is evaluated against your plan policies, we include all resources in the payload, including resources with no changes (no-ops).
What is changing?
Going forward, we will no longer include unchanged resources in the policy input data. For the vast majority of customers, this change will be invisible. Plan policies that check for planned changes to resources will continue to work exactly as before.
If your plan policies reference or inspect unchanged resources (no-ops), you may need to update your policy logic. We've proactively identified accounts that could be affected and will be reaching out directly.
Why is it changing?
For most stacks, no-op resources make up the large majority of the plan payload. Removing them significantly reduces the size of data processed during policy evaluation, which means faster policy evaluation and better overall performance.
When is it changing?
The gradual rollout will start on the 1th April 2026. Have questions? Feel free to reach out. We’re more than happy to answer a questions, and assist in any way we can.
March 18th, 2026

Today is a big day for us here at Spacelift. We’ve been working hard on some very exciting new functionality. Today, we are pleased to announce Spacelift Intelligence, a set of AI capabilities built directly into the Spacelift platform. It includes two components that work together: an AI Infrastructure Assistant we’re calling Infra Assistant and a natural language deployment model called Intent.
Why This, Why Now?
IaC and GitOps are still the right foundation for managing infrastructure. That's not changing. But those workflows were designed for production. As development velocity increases, especially for experiments, sandboxes, and POCs, the IaC and GitOps pipeline starts to get clogged. AI tools have accelerated the development cycle, but infrastructure hasn’t kept up.
Spacelift Intelligence is our answer to closing this new AI-velocity gap. The goal isn't to replace your Terraform code or your GitOps workflow. It's to give you an AI-native operations layer that gives your platform team the speed of AI without sacrificing the governance, visibility, and control you depend on.
Infra Assistant
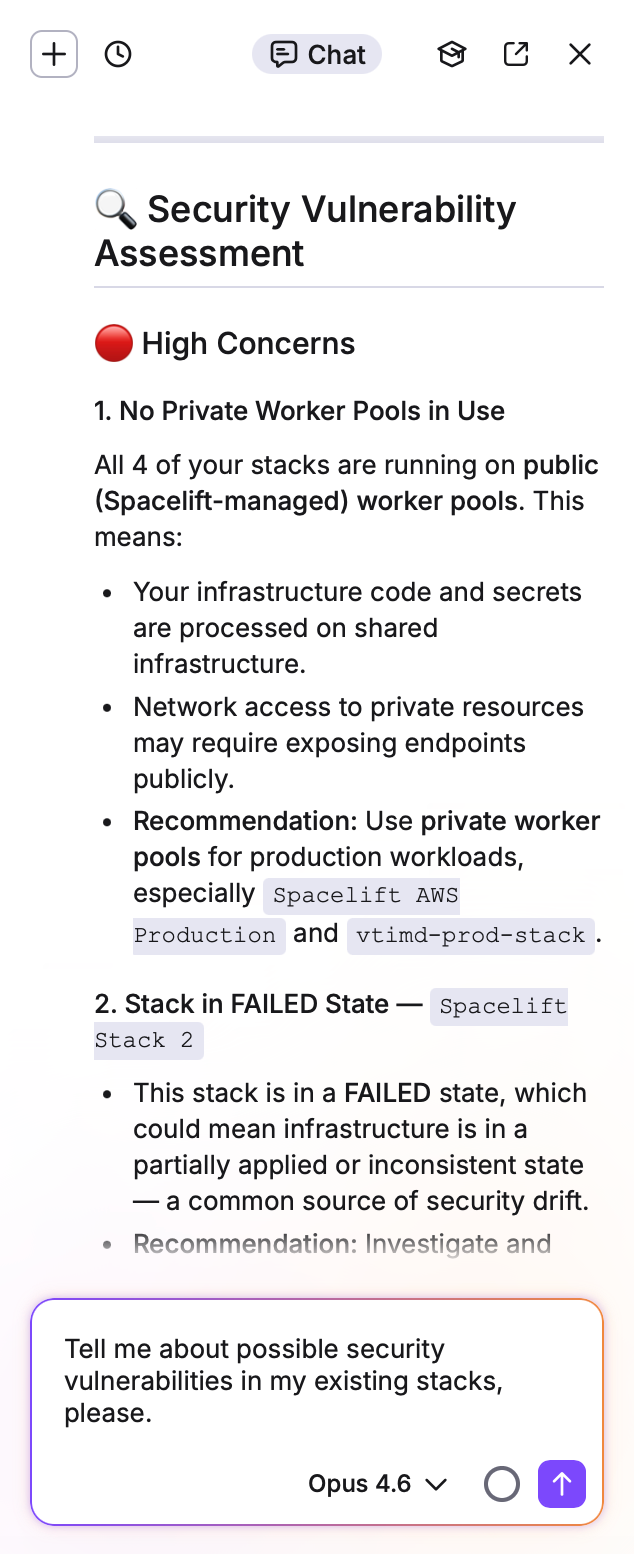
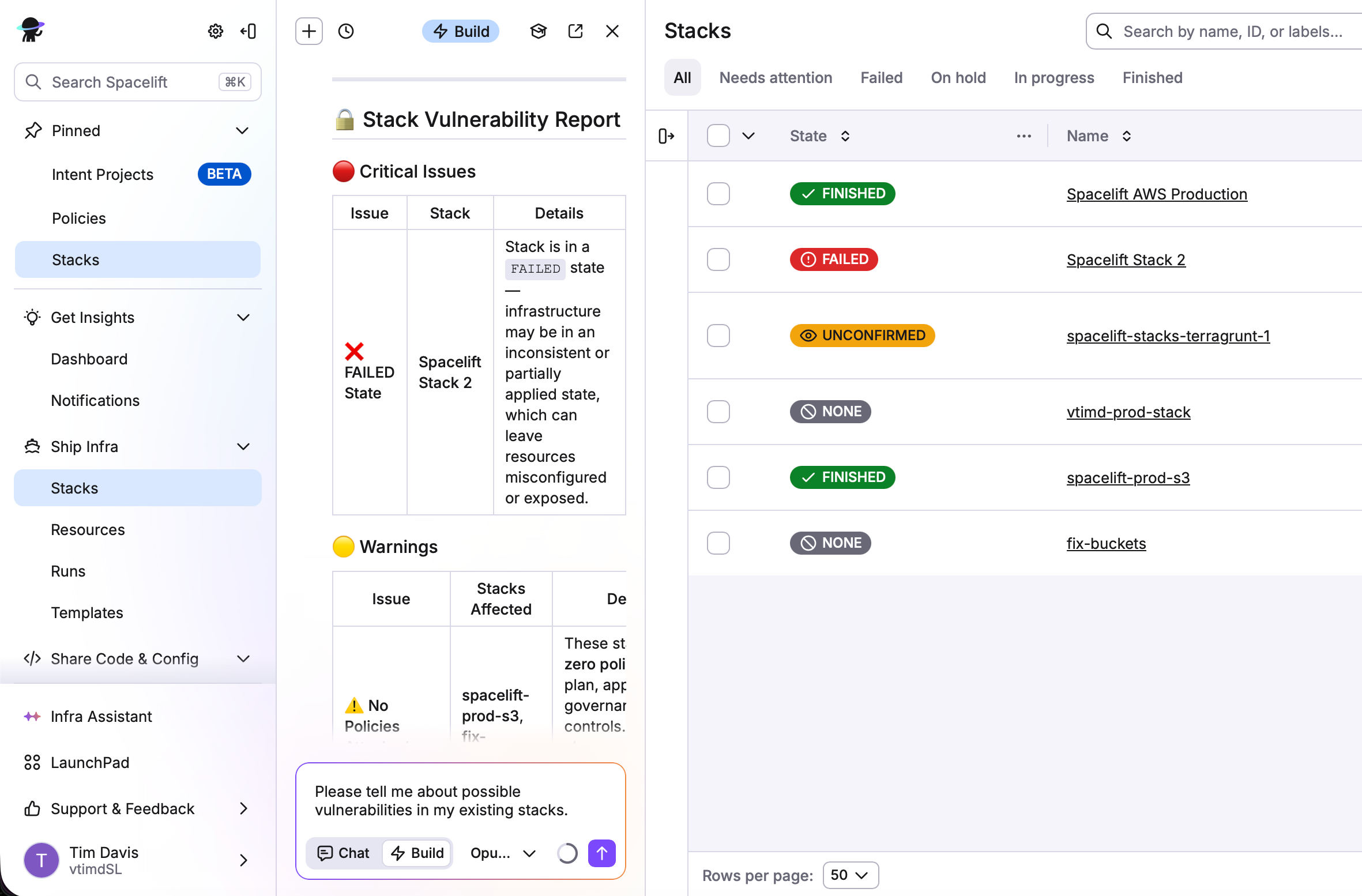
Infra Assistant is an AI chat interface embedded in Spacelift. You can ask it infrastructure-related questions and get guidance without leaving the platform.
“Please find any public s3 buckets across all my stacks”
“Do I have any CVE vulnerabilities in my environment?”
“What would you recommend I do to optimize my production deployments?”
Infra Assistant is context-aware, understands your stacks, runs, and the state of your infrastructure, so answers are grounded in your actual environment rather than generic documentation. Whether you're debugging a failed run, exploring a configuration change, or trying to understand what a proposed change will do, the assistant has the context to be useful.
Spacelift Intent
Spacelift Intent is AI-powered infrastructure provisioning through natural language. Rather than asking a question and receiving an answer or getting generated Terraform code, you describe what you want your infrastructure to do. Intent interprets that, translates it into the appropriate configuration, and acts on it. No code involved at all. Intent talks directly to the providers and deploys what you need, when you need it.
“I need an S3 bucket to store some temporary files. Adhere to any company policies.”
“Please create and test a policy to not allow public ec2 instances.”
“Please build 3 ec2 instances in us-west-1 so I can test a prototype.”
You speak it, and Spacelift Intent builds it. No code, no repository, no waiting. You can use Spacelift Intent by chatting with Infra assistant or have your developers connect their agent or LLM of choice to our MCP server.
Getting Started
Spacelift Intelligence is available now. For more information, check out the blog here. Also, sign up for the upcoming webinar where we will discuss Spacelift Intelligence in depth here, and see it in action here!
February 26th, 2026
Maybe you’ve seen this issue before. In complex organizations where multiple teams share a Spacelift account, spaces often end up with the same name in different branches of the hierarchy, like having a us-east-1 space under both production and staging. Without the ability to customize the subject claim, those spaces produce identical OIDC tokens, making it impossible for cloud providers like AWS, GCP, or Azure to tell them apart and apply the right permissions.
You can now customize the OIDC subject claim that Spacelift includes in tokens generated for cloud provider authentication. Previously, the subject claim was always built from the space slug, which caused a frustrating problem in hierarchical space structures: two spaces in different branches of your organization but with the same name, like /root/production/us-east-1 and /root/staging/us-east-1, would produce identical subject claims. That made it impossible to write cloud provider trust policies that distinguished between them.
The new subject template setting lets you define your own claim format using a set of available placeholders, including {spacePath}, which resolves to the full hierarchical path of the space. This unlocks two things that were not possible before: you can now differentiate between identically-named spaces in different branches, and you can write a single wildcard trust policy that covers an entire branch of your space hierarchy, like all production spaces, without needing to update the policy every time a new space is added. The setting is available in Organization Settings under Security, requires admin access, and comes with a migration guide to help you update existing trust policies without causing authentication failures during the transition.
You can read the full documentation here!
February 25th, 2026
Improvement
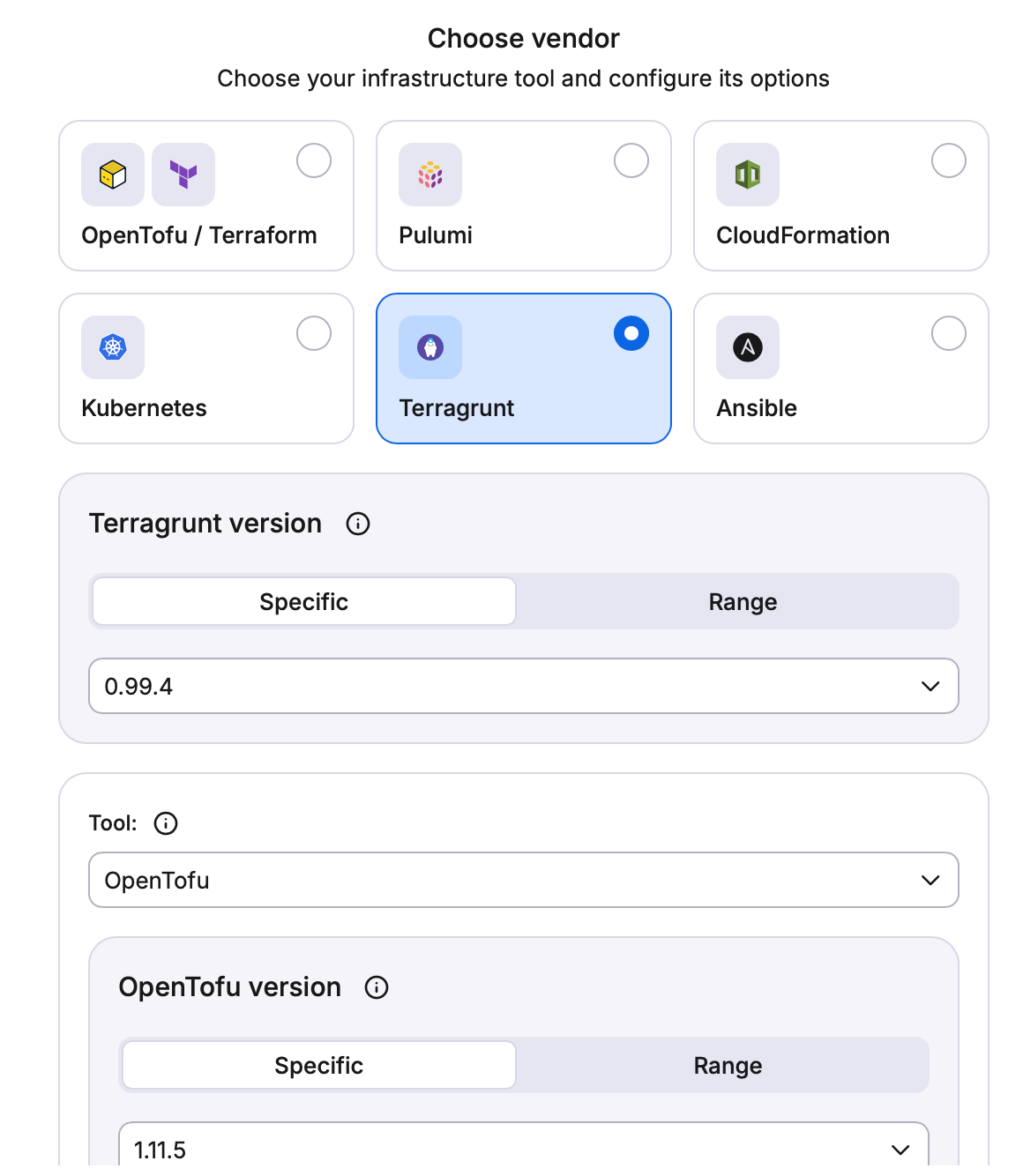
In our continued effort to bring you the best possible platform for your IaC management, today we are happy to announce that Terragrunt is now officially a first-class citizen in Spacelift! What does that mean exactly? The biggest news is that we now support native state management inside the platform. That means you can now let Spacelift do what Spacelift does best, while using your Terragrunt projects. Previously, you had to use remote state configurations if you wanted to use Terragrunt inside Spacelift, but not anymore.
This is a big win for all of our users, and provides even more options and flexibility when it comes to working with multiple frameworks across clouds. Be sure to give it a go, and let us know how you like it. Your feedback and input is critical for us.
Note: In the process of delivering the functionality for Spacelift to manage the state of Terragrunt projects natively, previously the behavior of selecting to “Delete Resources” when deleting a stack was that none of the resources would actually be removed. So whether you picked to keep or delete resources, they would simply remain. This non-expected behavior has now been remediated. Now, the expected behavior should be exactly what you select when deleting resources. When deleting the stack, resources will either stay or be deleted based on which option you select.
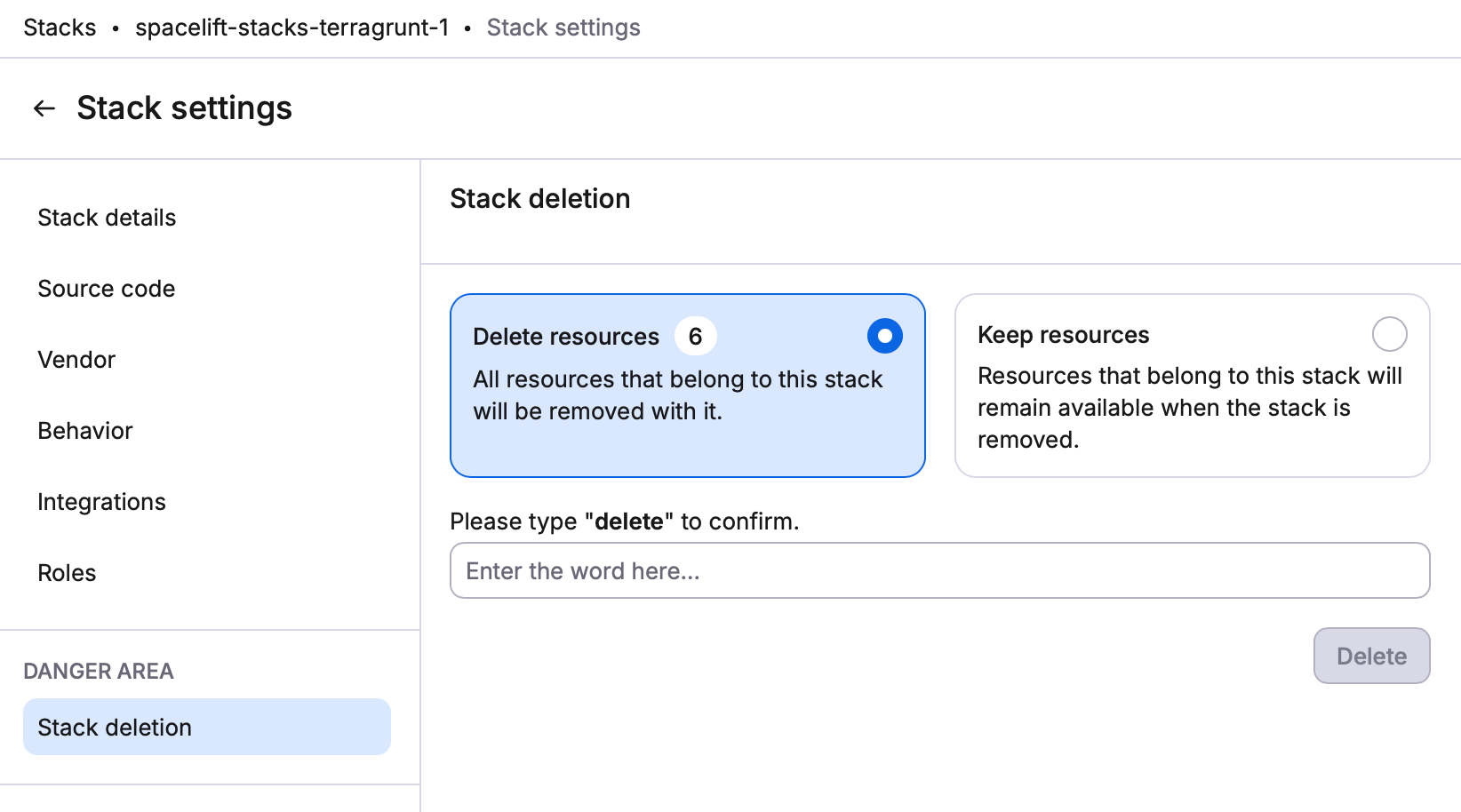
For more info on Terragrunt support in Spacelift, and to get started, check out the blog, video, and Documentation.
February 18th, 2026
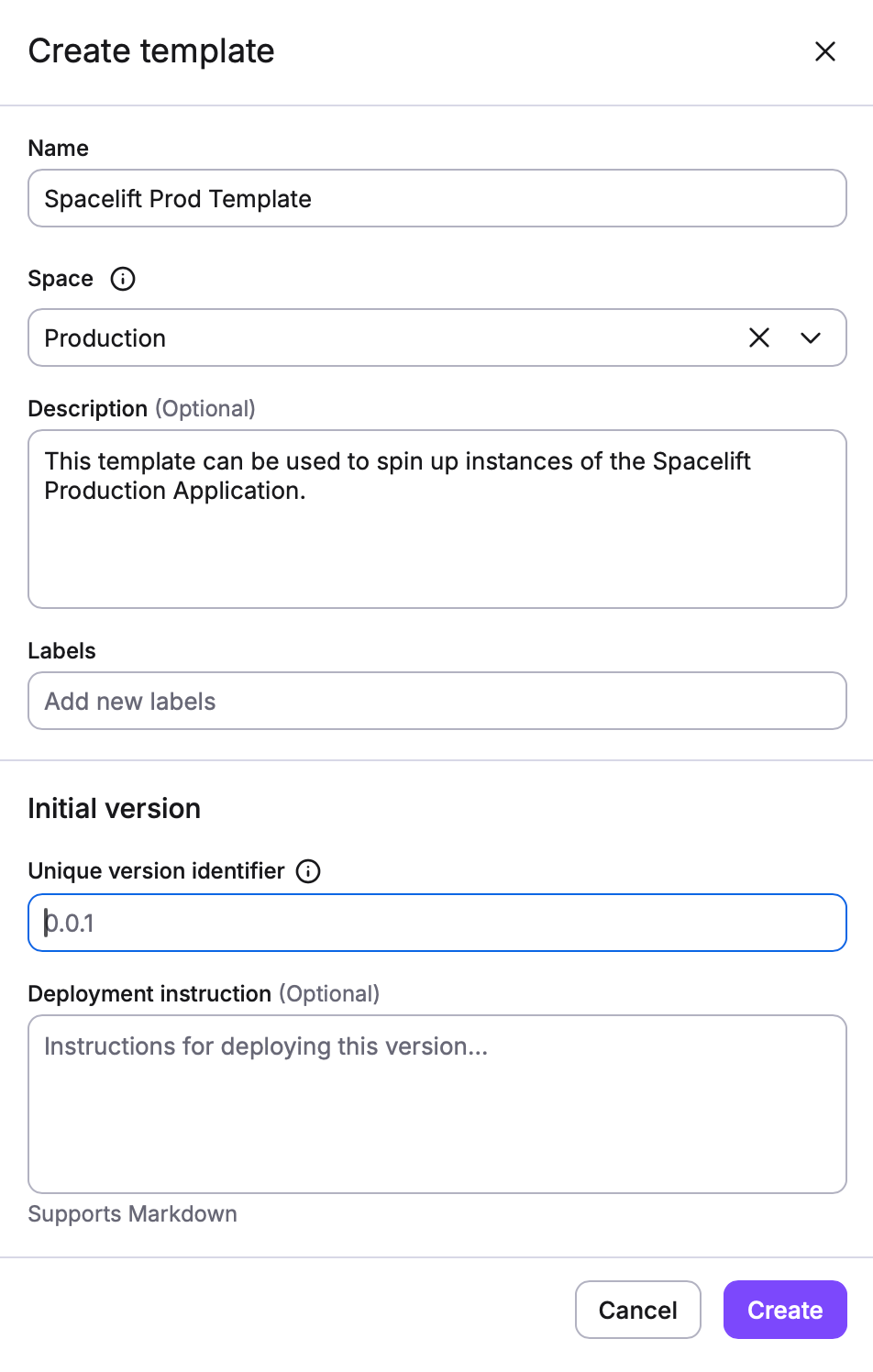
As always, you’ve been asking, and we’ve been listening. I’m sure you’re already very familiar with Blueprints in Spacelift. A Blueprint is like a template for a stack and its configuration. The blueprint contains variables that can be filled in by providing inputs when creating a stack from the Blueprint. The blueprint can also contain a list of other resources that will be created when the stack is created.
This is all well and good, but we really wanted to step it up a notch. And with that being said, I’d like to introduce you to Templates! Templates provide a self-service approach to infrastructure provisioning, making it easier for application developers to deploy infrastructure without deep IaC or Spacelift knowledge. Templates focus on enabling end users to deploy infrastructure through a simplified, form-based interface.
Now, I know what you’re thinking. That kinda sounds like Blueprints. But, while both features enable infrastructure provisioning, they have fundamentally different approaches and serve different use cases:
Blueprints are a creation tool that generates stacks which then live independently:
Creates stacks that become regular, fully editable Spacelift stacks
Once created, stacks can be modified manually like any other stack
No ongoing relationship between the blueprint and the created stacks
Stacks continue to evolve independently after creation
Blueprint changes don't affect previously created stacks
Templates are a lifecycle management tool that maintains control over deployed infrastructure:
Creates stacks through deployments that are fully managed by the template
Stacks created from templates are immutable - cannot be edited manually, even by admins
The only way to modify infrastructure is by:
Updating the template deployment to use a different version
Creating a new template version with changes and update deployment to use it
Modifying deployment inputs
Deployments maintain a permanent link to the template version
Templates ensure consistency across all deployments
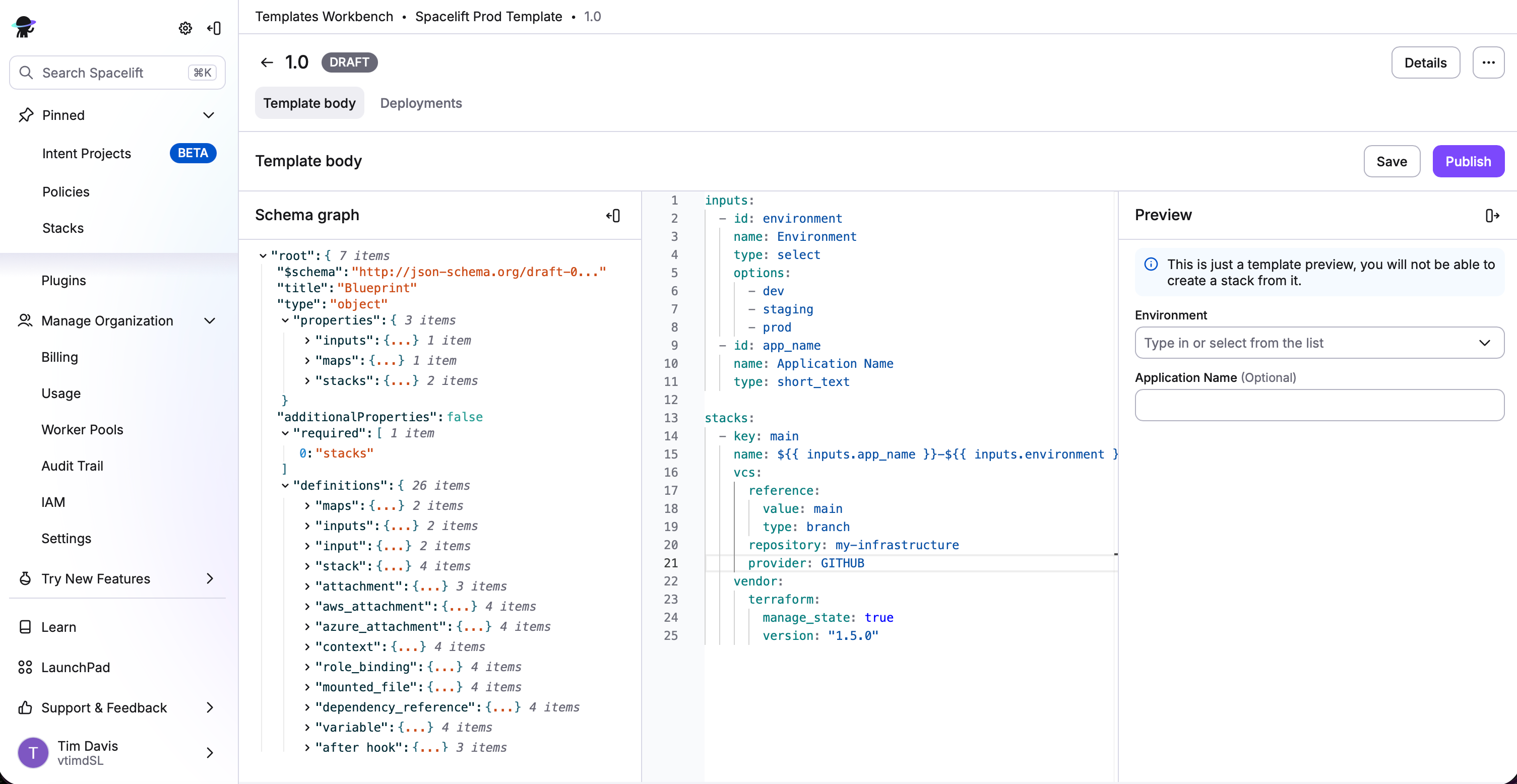
There are 2 main interfaces for Templates. The Templates Workbench is designed for platform teams and template authors. The Templates List is designed for application developers and end users.
Templates are now available for any customers with Business plans and above!
For more information, check out the documentation. And be sure to let us know how it goes. Your feedback is important to us!
January 13th, 2026
Happy New Year! We’ve been hard at work, back after a great holiday season. And now we’re ready to share a cool new update we have for module sharing permissions. Previously, to be able to share a module with a space, you needed the following permissions:
Admin access on the space where the module belongs, AND
Write access on the space where the module belongs
We know that it wasn’t exactly ideal to have to provide admin or write access to the entire space just for module sharing. We heard your requests, so now we are introducing a new action to advanced access. The SPACE_SHARE_MODULE control allows sharing a module with a space without giving admin or write access to the target space!
Note: that the role should be assigned to the space you want to share with, and not the space of the module itself.
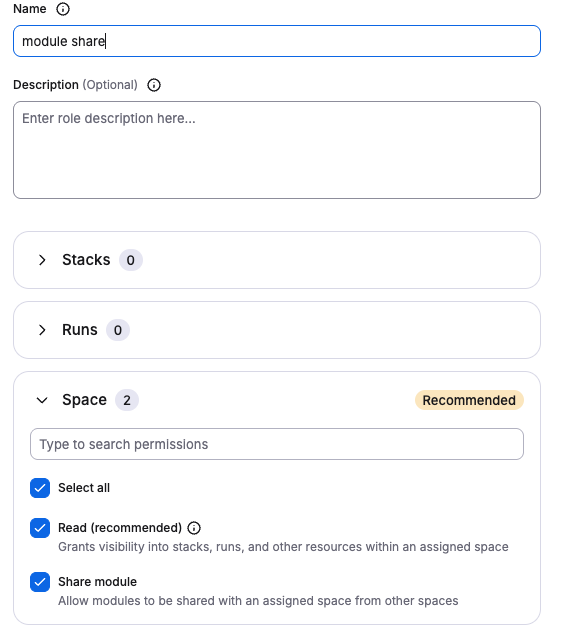
This was a highly requested feature, so we are really happy to deliver it to you. You can read more about module registry permissions in the documentation here. And, as always, your feedback is important to us. So take it for a spin, and let us know how you like it.
December 19th, 2025
Have you found yourself creating a new stack, and wish that your cloud integration would simply just be available and attach automatically? Your day has come. Auto-attach for cloud integrations is now GA in Spacelift!
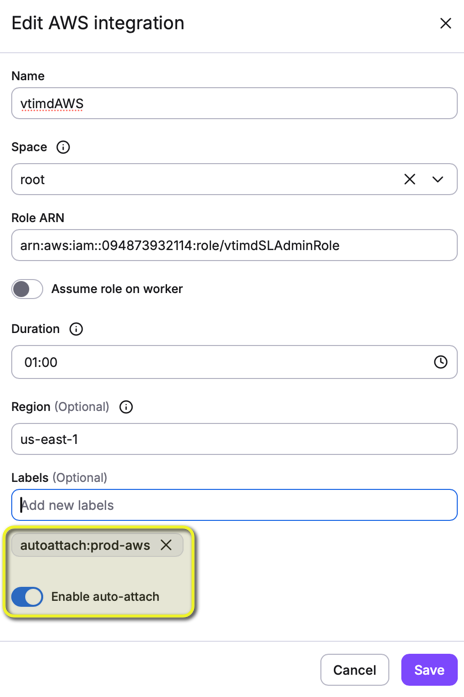
Whenever you create or edit a cloud integration, you can now toggle Enable auto-attach. Once that is done, just add a label to the integration that says autoattach:<your_label>. Any stack that has <your_label> on it will automatically attach the cloud integration. It is as simple as that!
This was one of the most requested features, so we are really happy to deliver it. Take it for a spin, and be sure to let us know what you think. We always want to hear from you.
For more info, check out the documentation here.